BYOD/eCOA in 2026: Timestamp Drift, Part 11/GDPR, and Audit Trails No One Wants to Own
Multi-device data capture brings clock drift and record-retention headaches. Learn how to align timestamps, Part 11, and GDPR compliance in one defensible plan.
The Failure Everyone Recognises but Nobody Documents
As clinical research evolves toward digital, remote, and patient-centric designs, Bring Your Own Device (BYOD) and electronic Clinical Outcome Assessments (eCOA) have become fixtures in modern trials. They promise convenience, real-time data capture, and scalability. But beneath the surface lies a complex web of compliance challenges—timestamp drift, audit trail ownership, and alignment with 21 CFR Part 11 and GDPR requirements. It started the way most compliance failures do—quietly.
A multinational Phase III eCOA study rolled out BYOD across 14 countries, collecting patient-reported outcomes on personal smartphones. The platform was validated. The vendor was reputable. The protocol was approved. And for 11 months, everything looked fine—until the data management team ran a routine timestamp reconciliation and discovered that device-level clock drift had reached up to 14 minutes on certain Android handsets [1].
Suddenly, diary entries fell outside protocol-defined visit windows. Dosing intervals looked inconsistent. And the audit trail—the single document that should have told the full story—was split across three systems, none of which agreed on who owned what.
This is not a hypothetical. It is a pattern. And it is accelerating as BYOD and eCOA adoption scales faster than the compliance infrastructure designed to support it [2,3].
The Fail: Three Fractures That Broke the Data Backbone
Fracture 1: Timestamp Drift — When Clocks Lie
Timestamp drift occurs when local device clocks diverge from server or regulatory reference times. In provisioned-device models, organisations enforce Network Time Protocol (NTP) synchronisation. In BYOD models, that control evaporates. Participants may disable automatic time settings, cross time zones, or simply never update their phone’s clock [5].
FDA’s 21 CFR Part 11 and EMA’s ALCOA+ principles require timestamps to reflect an accurate, unambiguous record of when data were created and modified [4]. A few minutes of drift may seem trivial—until those minutes shift a diary entry from “compliant” to “out-of-window.”
The cost: In the case above, sponsors had to manually reconstruct submission windows—a process that consumed over 200 person-hours and delayed database lock by six weeks.
Fracture 2: The Audit Trail Nobody Owns
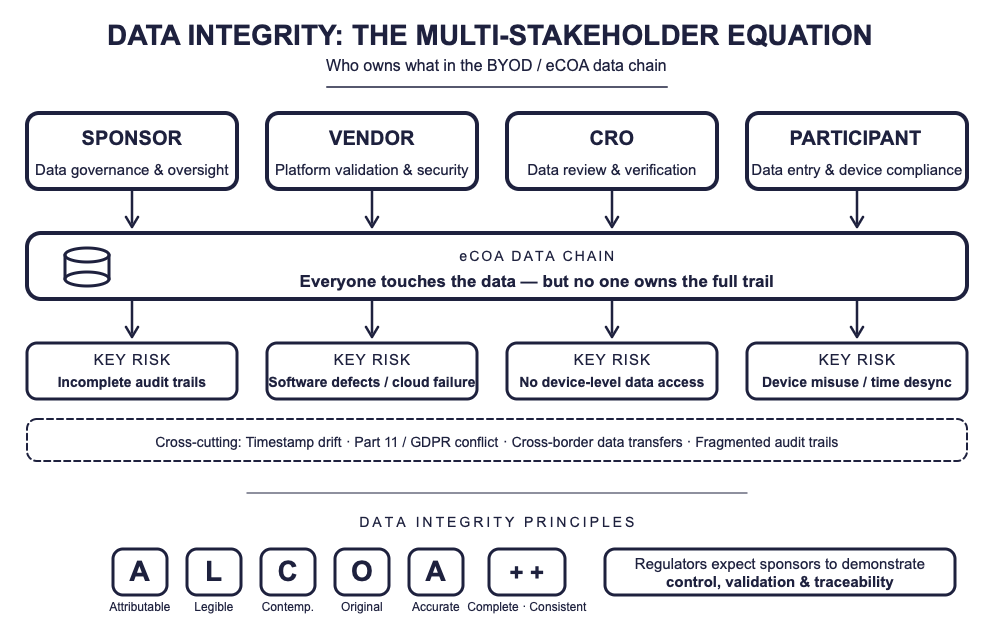
In a BYOD ecosystem, audit trail ownership becomes diffuse. Participants generate data on personal devices. Vendors host the eCOA platform and manage back-end infrastructure. Sponsors remain legally accountable under GCP and Part 11. CROs monitor data quality but rarely have device-level access [7].
The result: everyone touches the data, but no one owns the full trail.
Regulators expect the sponsor to retain audit-ready traceability—including device identifiers, timestamps, and user authentication logs—regardless of outsourcing arrangements. Inadequate audit trail integration between BYOD devices and vendor platforms has been flagged in FDA and MHRA inspections since 2023 [8].
The cost: One CRO reported that assembling a complete audit trail for a single BYOD study required extracting logs from four separate vendor systems, reconciling conflicting metadata formats, and producing a unified narrative—after the inspection had already been announced.
Fracture 3: Part 11 and GDPR — The Dual Compliance Collision
Part 11 demands retention, traceability, and validation. GDPR demands minimisation, consent, and the right to erasure. In BYOD trials, both frameworks collide head-on [9,10].
Device-level data may include personal metadata—device IDs, IP addresses, geolocation. Participants who withdraw consent may trigger data deletion obligations that conflict with Part 11 retention requirements. Cloud-based vendors processing data across jurisdictions introduce cross-border transfer risks [10,11].
The cost: A European sponsor discovered post-study that their eCOA vendor had been routing audit log backups through a US-based cloud provider without adequate Standard Contractual Clauses—a GDPR violation that required retroactive Data Protection Impact Assessments and regulator notification.
The Fix: One Defensible Plan
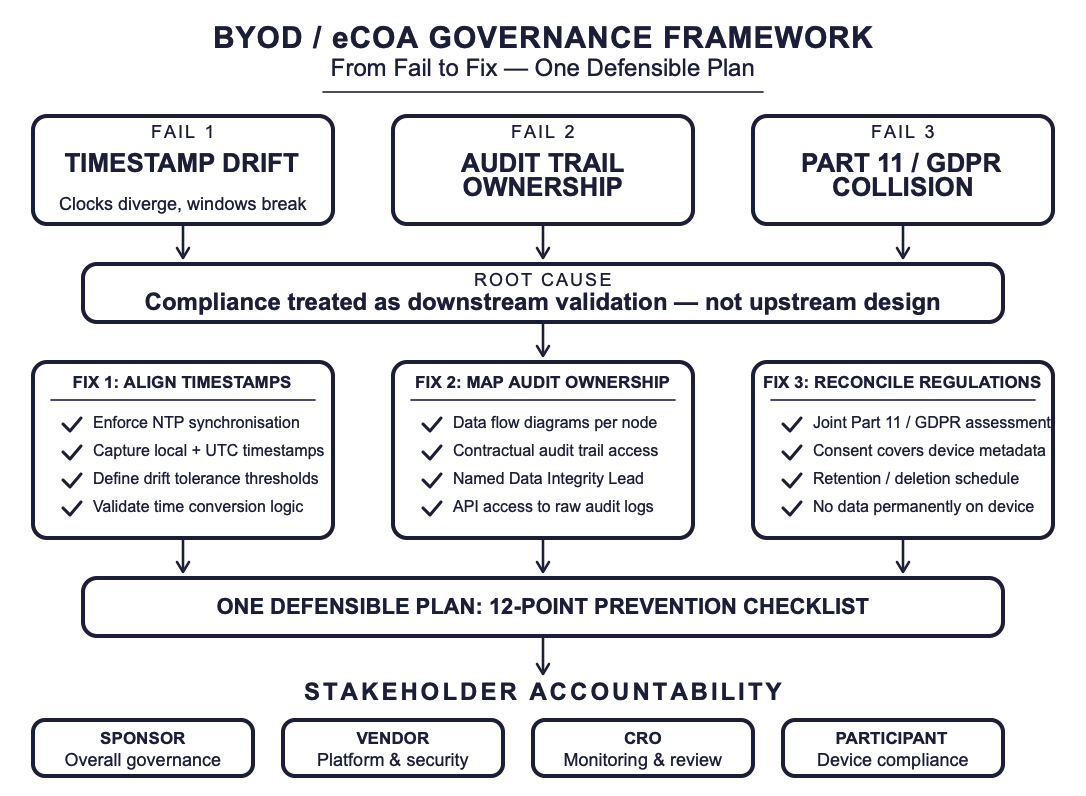
The failures above share a common root cause: compliance was treated as a downstream validation activity rather than an upstream design principle. The fix requires integrating timestamp governance, audit trail architecture, and privacy controls into a single, defensible plan from Day 1.
Fix 1: Align Timestamps Before You Collect Data
Enforce automatic network time synchronisation as a prerequisite for app activation. Capture both local device time and Coordinated Universal Time (UTC) in every audit trail record. Validate time conversion logic during system qualification testing—not after data collection begins [4,5].
Implementation: Configure eCOA platforms to flag and log any device where automatic time settings are disabled. Build drift tolerance thresholds into your Data Management Plan (e.g., ±2 minutes) and define escalation procedures for deviations.
Fix 2: Map Audit Trail Ownership Before You Outsource
Create a data flow diagram that traces every eCOA data point from device to database, identifying the responsible party at each transition. Establish contractual provisions ensuring sponsor access to complete, unaltered audit trails [7,12].
Implementation: Include audit trail specifications in vendor qualification. Require vendors to provide API-based access to raw audit logs—not just summary reports. Assign a named Data Integrity Lead responsible for end-to-end trail reconciliation.
Fix 3: Reconcile Part 11 and GDPR at the Protocol Level
Integrate privacy-by-design and validation-by-design principles from the earliest stages of eCOA system selection and configuration [9,11]. Define, in the protocol and informed consent, exactly which device metadata will be collected, how long it will be retained, and under what conditions it may be deleted or anonymised.
Implementation: Conduct a joint Part 11/GDPR impact assessment during eCOA vendor selection. Ensure that consent forms explicitly address the use of personal devices and metadata. Build data retention and deletion schedules that satisfy both frameworks without contradiction.
Prevention Checklist: Never Fail This Way Again
The following checklist consolidates the remediation steps into a reusable pre-study audit:
| ✓ |
Checklist Item |
Owner |
|---|---|---|
| □ | Automatic NTP synchronisation enforced on all BYOD devices | IT / Vendor |
| □ | Dual timestamp capture (local + UTC) in every audit record | eCOA Vendor |
| □ | Drift tolerance threshold defined in Data Management Plan | Data Management |
| □ | Data flow diagram mapping audit trail ownership at every node | Sponsor / DI Lead |
| □ | Contractual provisions for sponsor access to raw audit logs | Legal / Vendor Mgmt |
| □ | Named Data Integrity Lead for end-to-end trail reconciliation | Sponsor |
| □ | Joint Part 11/GDPR impact assessment during vendor selection | Regulatory / Privacy |
| □ | Consent forms address personal device and metadata use | Regulatory Affairs |
| □ | Data retention/deletion schedules reconciling both frameworks | Privacy / QA |
| □ | No sensitive data stored permanently on personal devices | IT Security / Vendor |
| □ | System qualification includes time conversion logic testing | Validation Lead |
| □ | Risk-based monitoring covers digital systems, not just sites | Clinical Ops / QA |
Lessons Learned
1. Compliance is a design decision, not a validation activity. If timestamp governance, audit trail mapping, and privacy controls are not embedded in eCOA platform selection criteria, they will become expensive remediation projects post-inspection.
2. BYOD does not eliminate device management—it distributes it. Sponsors trade provisioning costs for governance complexity. The savings are real; so are the risks [2,3].
3. The device may belong to the participant, but the responsibility belongs to the sponsor. Outsourcing execution does not outsource accountability. Regulators are increasingly clear on this point [1,7].
4. Part 11 and GDPR are not opposites—they are complementary constraints. A well-designed data governance plan can satisfy both frameworks without contradiction. The key is addressing them together, at protocol level, rather than in parallel silos [9,10].
5. Digital accountability is the new regulatory expectation. FDA’s 2023 DHT guidance and EMA’s draft guideline on electronic systems signal that sponsors must demonstrate control, validation, and traceability—regardless of where or how data originate [1,5].
Conclusion: Own the Digital Backbone
The digital era has made clinical research more connected but also more fragmented. BYOD and eCOA approaches unlock access, scalability, and engagement—but they also multiply risks that traditional compliance frameworks were never designed to handle.
The failures described here are not edge cases. They are patterns. And they are preventable—if sponsors invest in upstream governance rather than downstream remediation.
In decentralized trials, the device may belong to the participant, but the responsibility belongs to the sponsor. The question is not whether you will face these challenges—it is whether you will have a defensible plan when you do.
References
1. FDA. Digital health technologies for remote data acquisition in clinical investigations. Guidance. 2023.
2. Aryal S, Goldsack JC, Izmailova E, et al. Patient centricity in digital measure development. NPJ Digit Med. 2024.
3. EFPIA. Reflection paper on integrating medical devices into medicinal product clinical trials. Brussels: EFPIA; 2025.
4. FDA. Part 11, electronic records; electronic signatures — Scope and application. Guidance. 2003.
5. EMA. Guideline on computerised systems and electronic data in clinical trials. Draft, 2023.
6. Bent B, Goldstein BA, Kibbe WA, Dunn JP, et al. Investigating sources of inaccuracy in wearable optical heart rate sensors. npj Digital Medicine 2020;3:18.
7. ICH. E6(R3) Good Clinical Practice draft guideline. International Council for Harmonisation; 2023.
8. MHRA. Inspection findings summary for electronic systems in trials. London: MHRA; 2024.
9. European Commission. General Data Protection Regulation (GDPR). Brussels: EC; 2016.
10. European Data Protection Board. Guidelines on clinical research under GDPR. Brussels: EDPB; 2023.
11. ISO 27001:2022. Information security, cybersecurity, and privacy protection. Geneva: ISO; 2022.
12. Kellar E, Bornstein S, Celi LA, et al. Optimizing the use of electronic data sources in clinical trials. Ther Innov Regul Sci. 2017;51(4):408–416.